Access Azure File Shares Without Port 445 or VPN
Azure File Shares were built for SMB. Remote access was an afterthought. Your users need a mapped drive, a browser, and mobile access over HTTPS. No VPN tunnels. No blocked ports. Just a gateway to the file shares you already have.
Users get the same mapped drive experience. IT eliminates VPN overhead and gains a full audit trail.

Azure Files Are Cloud-Ready. Remote Access Is Not.
Azure File Shares use SMB. That works on a LAN. The moment users go remote, you hit a wall.
Port 445 is blocked by most ISPs
SMB requires port 445. Most residential and many commercial ISPs block it. Users cannot map Azure File Shares from home or remote offices without a tunnel.
VPN tunnels multiply complexity
Site-to-site VPN from Azure to each office. Per-user VPN for remote workers. VPN gateways, split tunneling, help desk tickets. The overhead scales with your workforce.
Users avoid what does not work
VPN drops, slow connections, and confusing reconnections push users to workaround tools. Shadow IT grows. IT loses visibility. Audit gaps widen.
Three Ways To Connect. Choose What Fits Your Environment.
MyWorkDrive connects directly to Azure File Shares. No file copies. No sync layer. Your deployment model determines which method works best.
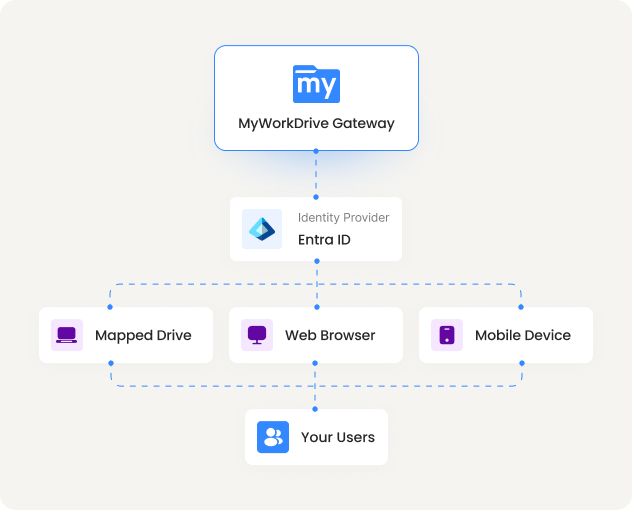
Entra ID over API
Connect directly using Entra ID authentication over REST API. No Active Directory domain controllers required. The most streamlined path for cloud-native environments.
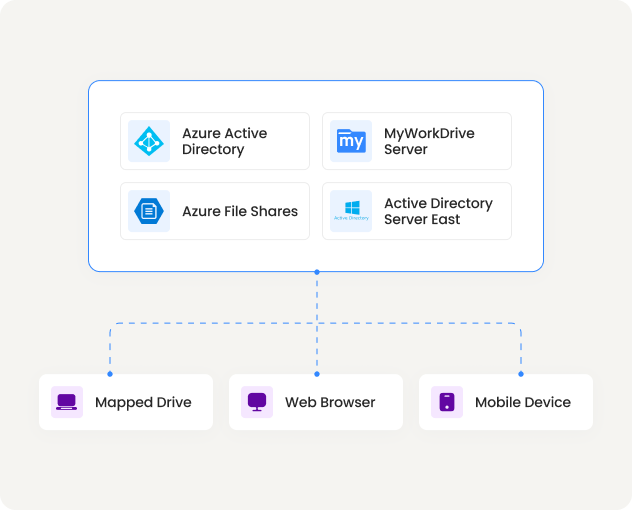
Active Directory Over SMB
For organizations with existing AD infrastructure. MyWorkDrive connects to domain-joined Azure File Shares over SMB using Kerberos. Preserves your current NTFS permission model.
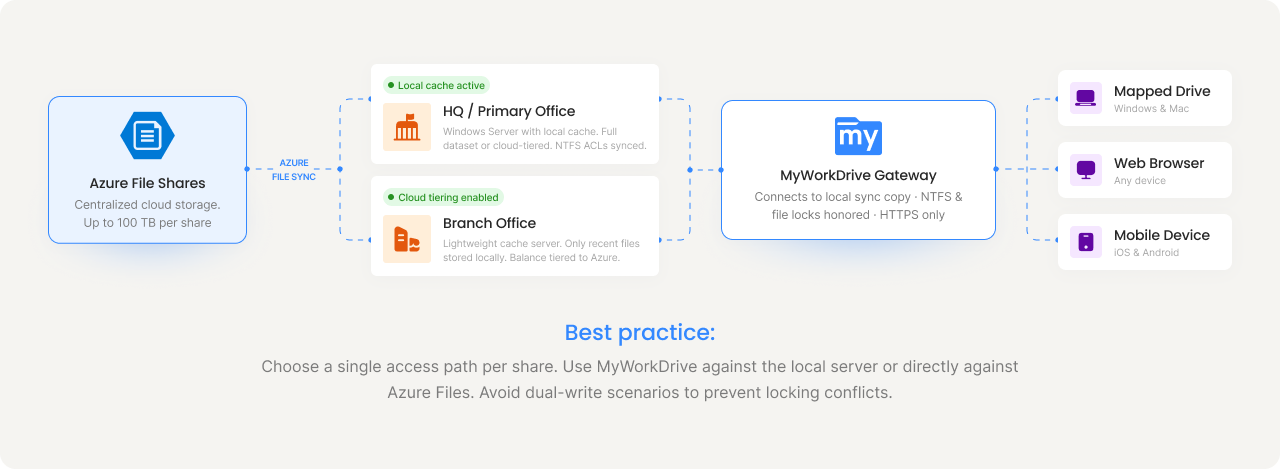
Azure File Sync (Hybrid)
For organizations bridging on-premise and cloud. Azure File Sync replicates files between local servers and Azure File Shares. MyWorkDrive connects to the local sync copy with full NTFS ACL support.
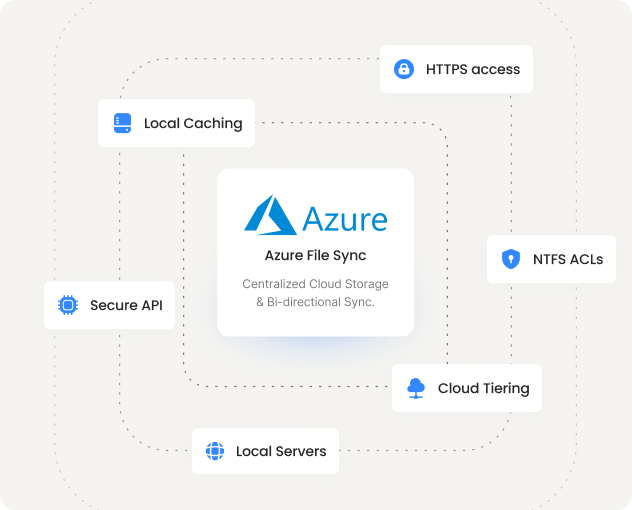
Multi-site Access With Azure File Sync.
For organizations that still have on-premise servers, Azure File Sync bridges the gap. MyWorkDrive connects to the local sync copy. From its perspective, nothing has changed.
Bi-directional sync
Changes on-premise replicate to Azure. Changes in Azure replicate back. Write-back keeps both sides current.
Multi-site caching
Place a cache at each branch office. Centralized storage in Azure. Users at every location get local-speed file access.
Cloud tiering
Set capacity limits per server. Recent files stay local. Older files tier to Azure File Shares automatically. Full namespace visibility remains.
NTFS ACLs preserved
Azure File Sync inherits and enforces NTFS permissions across all synced files and folders. Your permission model stays intact.
One File Share. Three Ways To Reach It.
Every user gets the client that fits their workflow. IT manages one policy layer across all three.
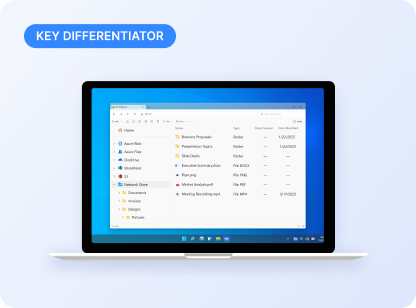
Mapped Drive Client
Windows and Mac users get a familiar network drive letter over HTTPS. Files open natively in desktop apps. No VPN. No port 445.
Users: "It works exactly like my old network drive."
IT: Centrally managed, policy-enforced, fully audited.
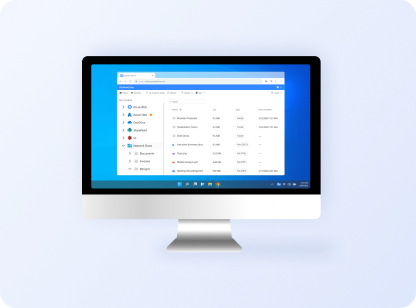
Web File Manager
Access from any browser on any device. No client install, no domain join. Authenticate with Entra ID or AD credentials.
Users: "I can get to files from any computer."
IT: Zero endpoint footprint. DLP controls still apply.
Mobile Apps
iOS and Android apps give field workers, executives, and remote teams file access from phones and tablets.
Users: "I can pull up files on site."
IT: Device approval and view-only mode available.
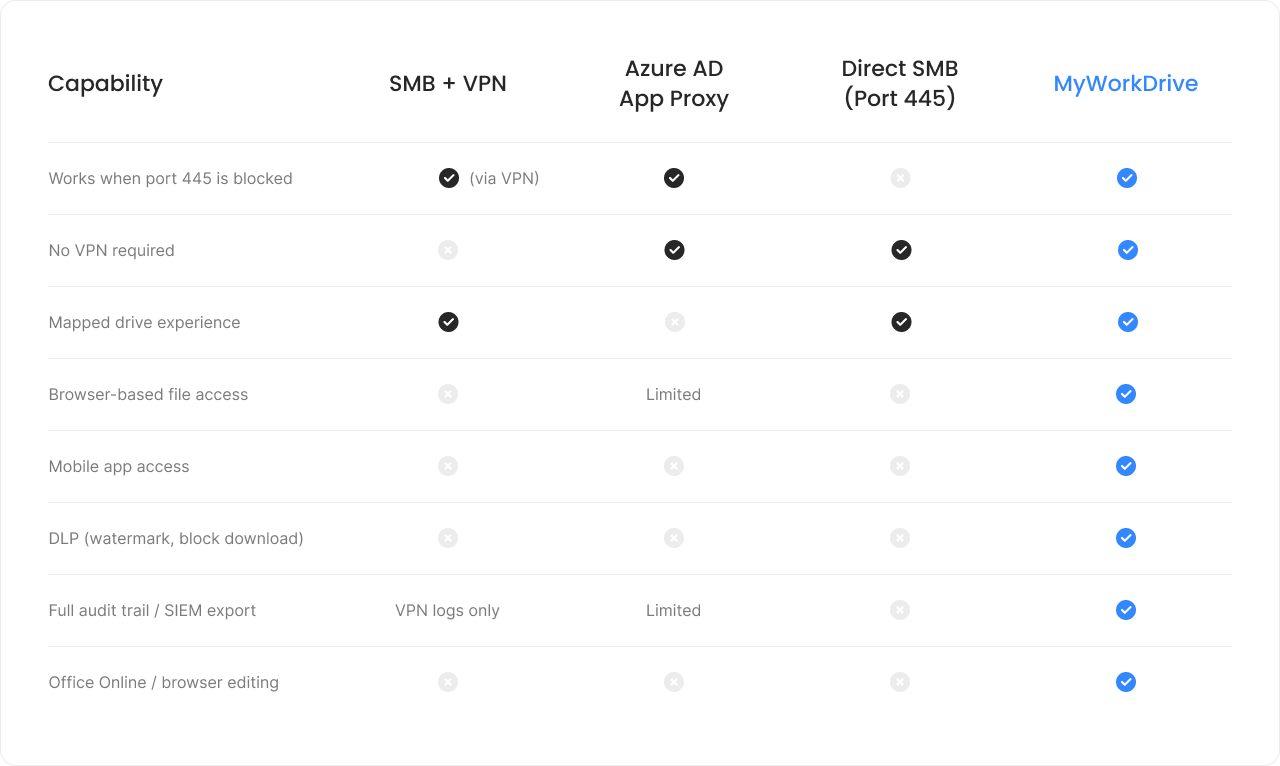
How Else Could Your Users Access Azure Files Remotely?
The native options for remote Azure File Share access all have significant limitations for everyday users.
Your Permissions. Your Control.
Enforced, Not Replaced.
MyWorkDrive does not create a parallel permission system. It enforces what you have already configured in AD, Entra ID, and your Azure File Shares.
Your identity provider stays authoritative
Authentication flows through AD, Entra ID, or SAML. MFA, Conditional Access, and session policies are enforced where you already manage them.
NTFS and share permissions honored
Whether connecting via SMB or API, existing permission structures are respected. No parallel ACL to manage. No permission drift to debug.
DLP controls for sensitive files
Block downloads, apply watermarks, restrict clipboard access, and enforce view-only mode. Configurable per share, per user group.
Audit every access event
Every file open, download, edit, and share is logged. Export to your SIEM for compliance reporting. HIPAA, GDPR, and CMMC-ready.
MyWorkDrive cannot elevate permissions. It can only enforce what is already granted in your storage and identity systems, and optionally restrict
further by policy. NTFS permissions, share permissions, and Entra ID access controls remain authoritative. Your existing source of truth stays in control.
Deploy In Hours. Not Months.
< 2 Hrs
Average deployment time
0
Files migrated
443
The only port you need
$5
Per user / month starting
Azure File Shares
Access, Answered.
Can I access Azure File Shares without a VPN?
Yes. MyWorkDrive connects to Azure File Shares over HTTPS (port 443) and presents them to users as a mapped drive, web file manager, or mobile app. No VPN tunnel, no port 445 exposure.
Do I need Active Directory or can I use Entra ID?
Both work. For cloud-native deployments, MyWorkDrive supports native Entra ID authentication over REST API with no AD domain controllers required. For existing AD environments, it supports domain-joined Azure File Shares over SMB with Kerberos.
How does MyWorkDrive handle NTFS permissions on Azure Files?
When connected via SMB to domain-joined Azure File Shares, MyWorkDrive fully honors NTFS ACLs. When connected via API with Entra ID, share-level permissions are managed through Entra ID roles. MyWorkDrive cannot elevate permissions beyond what is already granted.
Is MyWorkDrive a storage product or does data stay in Azure?
Data stays in your Azure File Share. MyWorkDrive is a gateway. It does not copy, sync, or store your files. Backup, compliance, and retention workflows continue to work as-is. There is no vendor lock-in.
Can I use Azure File Sync with MyWorkDrive?
Yes. If you have Azure File Sync replicating files to a local Windows Server, you can point MyWorkDrive at the local sync copy. NTFS ACLs are preserved. For best results, choose a single access path per share to avoid file locking conflicts between on-premise and cloud copies.
Can users edit Office files in the browser?
Yes. MyWorkDrive supports browser-based editing via Office Online and OnlyOffice. Files opened through the mapped drive client open natively in desktop Office applications. File locking prevents conflicts during concurrent edits.
What about Azure Files pricing tiers?
Azure Files offers Standard (HDD) and Premium (SSD) tiers. When connecting over API, MyWorkDrive removes the SMB overhead, which can allow you to use lower storage tiers with acceptable performance. Premium tiers are recommended for heavy workloads or large file access over SMB. Combined with MyWorkDrive at $5/user/month, the total cost is significantly lower than VPN infrastructure.
Map your Azure File Shares In minutes.
Start a free 14-day trial. Point MyWorkDrive at your Azure File Shares and give your users mapped drive, browser, and mobile access without a VPN.